"How secure are the access control readers you’re recommending to customers?"
It's a question integrators are hearing more often as security breaches make headlines. And while IT departments focus on firewalls and network security, the physical devices mounted on walls throughout a facility can become an overlooked vulnerability.
The challenge? Many readers on the market today were designed with convenience in mind, not security. When you're specifying systems for financial institutions, healthcare facilities, government agencies, or enterprise campuses, that's simply not good enough.
According to the IBM Cost of a Data Breach Report 2025, the average cost of a data breach was $4.4 million dollars. And while cyber attacks get most of the attention, physical security compromises can be just as devastating. A single compromised reader can grant unauthorized access to secure areas, expose sensitive data, or put people's safety at risk.
The answer to that opening question isn't a single security feature. It's multiple layers of protection working together. Let's take a closer look at what real access control reader security looks like, and why it matters for every installation you design.
What Makes a Reader Truly Secure?
At Wavelynx, our approach to reader security is simple: multiple independent layers of protection. If one layer is somehow compromised, the others continue to protect the system. Think of it as a vault within a vault. Each layer serves a distinct purpose in keeping your client's facility secure.
Here's what that looks like in practice:
Layer 1: Hardware-Based Encryption (The Vault)
The foundation of Wavelynx’s APEX Reader security is the EAL6+ certified secure element chip. This isn't just a processor. It's a dedicated cryptographic computer inside every reader.
This secure element stores encryption keys in tamper-resistant hardware. All encryption and decryption operations happen internally within the chip, which means keys never exist in accessible memory. Even if someone physically opened the reader, they couldn't extract them.
This is fundamentally different from software-based security. It's like having a bank vault with a computer inside every reader, one that's been certified to one of the highest security standards possible (EAL6+).
Why does this matter for integrators? Because you're not just protecting against network threats. You're protecting against physical attacks. Even if an attacker gains access to the reader's internals, the encryption keys remain locked away in dedicated hardware.
Layer 2: Encrypted Communication (OSDP)
Hardware security means nothing if the communication between reader and panel is exposed. That's where OSDP (Open Supervised Device Protocol) comes in.
Unlike legacy Wiegand protocol, which transmits data in unencrypted plain text, OSDP Secure Channel uses AES-128 encryption to protect every transmission between reader and controller. This prevents wire-tapping attacks where someone could place a "sniffing" device on the wiring to steal credential data.
But here's what makes this particularly valuable for integrators: Wavelynx readers feature OSDP Auto-Detect. The reader starts in listening mode and will switch to OSDP or Wiegand depending on what kind of signal is received from the panel. When the reader receives an OSDP message, it will switch to OSDP and further lock into OSDP-only mode when a Secure Channel is established.
This saves you significant time and labor costs on installations, while ensuring the transition to secure communication is seamless.
Layer 3: Physical Tamper Detection
Network security and encryption are critical, but what happens when someone tries to physically compromise the reader itself?
Wavelynx APEX readers include accelerometer-based tamper detection that monitors for unauthorized movement or attempts to remove the reader from the wall. Unlike traditional tamper switches that can be bypassed, the accelerometer detects even subtle movements like prying or shaking.
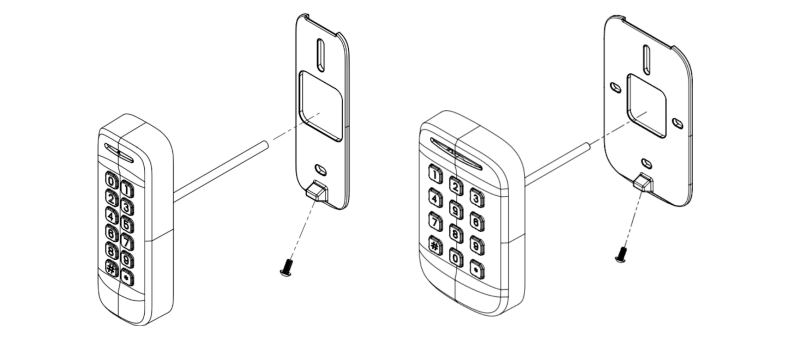
When tampering is detected, the reader immediately signals the access control panel via a dedicated "Tamper Out" wire, alerting security personnel in real-time. Combined with optional pin-in-torx security screws and a sturdy cast-metal mounting plate, these readers are designed to resist physical vandalism and unauthorized removal.
For installations in high-risk areas or outdoor environments, this layer of protection can make the difference between a security incident and a prevented breach.
Layer 4: Transition Security (Prox Filter)
Here's a security gap many integrators don't think about: What happens during a phased transition from legacy credentials to modern ones?
If you're using dual-technology credentials and multi-technology readers that support both prox (125 kHz) and smartcards (13.56 MHz), there's a vulnerability window. Until you've fully transitioned and disabled prox support on every reader, the insecure prox side of those credentials remains active. This creates a downstream attack vector as the prox side can still be exploited.
Wavelynx's Prox Filter feature solves this. Once enabled, the reader will never accept data from the prox side of the new dual-tech credential, even though it technically has the capability to read it. This means you can issue dual-tech credentials immediately, and you won't need to reconfigure each reader after the transition is complete.
For large installations with hundreds or thousands of readers, this saves substantial time and labor costs while closing security gaps during the transition period.
Why Platform Matters: Learning from History
When specifying readers, it's worth examining the track record of the underlying technology platform. Not all credential platforms are created equal, and history has shown which ones hold up under real-world attacks.
The NXP MIFARE DESfire platform that powers Wavelynx credentials has been deployed in millions of high-value transactions worldwide without a successful breach. Compare that to other platforms that have experienced well-documented encryption vulnerabilities and compromises.
For integrators, this matters because you're not just installing a reader. You're recommending a security platform that your clients will depend on for years. Choosing a platform with a proven track record means fewer callbacks, fewer emergency replacements, and more confidence in the systems you design.
Beyond Security: Built for Real-World Installation
Security layers are only effective if the reader is practical to install and maintain. Wavelynx APEX readers are designed with integrators in mind:
- Wide voltage range (5-24V) reduces the risk of frying readers during installation
- Angled security screws and metal backplate simplify mounting while enhancing physical security
- IP65+ rating provides weather and dust resistance for outdoor installations
- OSDP Auto-Detect eliminates manual configuration when transitioning protocols
These features don't just make installation easier. They reduce the likelihood of errors that could compromise security or create callbacks.
What This Means for Your Installations
As an integrator, your reputation depends on designing systems that work reliably and keep your clients secure. Reader security is no longer optional. It's a fundamental requirement, especially as compliance standards tighten and security threats evolve.
When you specify Wavelynx readers, you're not just choosing a product. You're choosing a multi-layered security approach that protects against both physical and cyber threats, simplifies transitions, and reduces long-term costs for your clients.
Whether you're designing a new system from the ground up or managing a phased transition from legacy technology, understanding these security layers gives you the confidence to have informed conversations with your clients about what real reader security looks like and why it matters.
Ready to Learn More?
Every installation is different, and choosing the right readers depends on your client's unique needs, budget, and existing infrastructure. If you're planning a transition from legacy systems or specifying readers for a new project, we'd love to help you explore your options.
Download our free guide: "Leaving Outdated Security Behind" to learn more about:
- The full access control ecosystem
- Emerging credential technologies
- The four primary transition strategies
- Hidden costs and how to avoid them
Or schedule a consultation with our team to discuss your specific project needs.



.png)


.png)