The industry has been stuck in a paradox for two decades. The new, modern standard has finally arrived.
Every technology goes through cycles. Innovation, adoption, maturity, decline. But access control has been unusual. It's been stuck with the same technology for 20 years.
Walk into most office buildings, hospitals, universities, or financial institutions today, and you'll encounter the same authentication technologies that were state-of-the-art in 2005. Wiegand systems. Prox cards and readers. Legacy encryption standards that have been compromised for years.
For these institutions, the consequences are real. Managing aging infrastructure demands increasing operational overhead—constant monitoring, patches, and workarounds. The security risk compounds annually. Known vulnerabilities create a persistent target that sophisticated attackers actively exploit. And with no meaningful security innovation possible, these organizations operate under a model of security by obscurity, hoping that their aging systems simply won't be targeted because newer systems exist elsewhere. It's a fragile position built on hope, not architecture.
It's not because these technologies work well. It's because the switching costs became so prohibitive that replacement felt impossible. Organizations found themselves locked in, not by choice, but by circumstance.
This is the story of how an entire industry became trapped by its own infrastructure.
The Paradox: Everyone Knew Change Was Needed
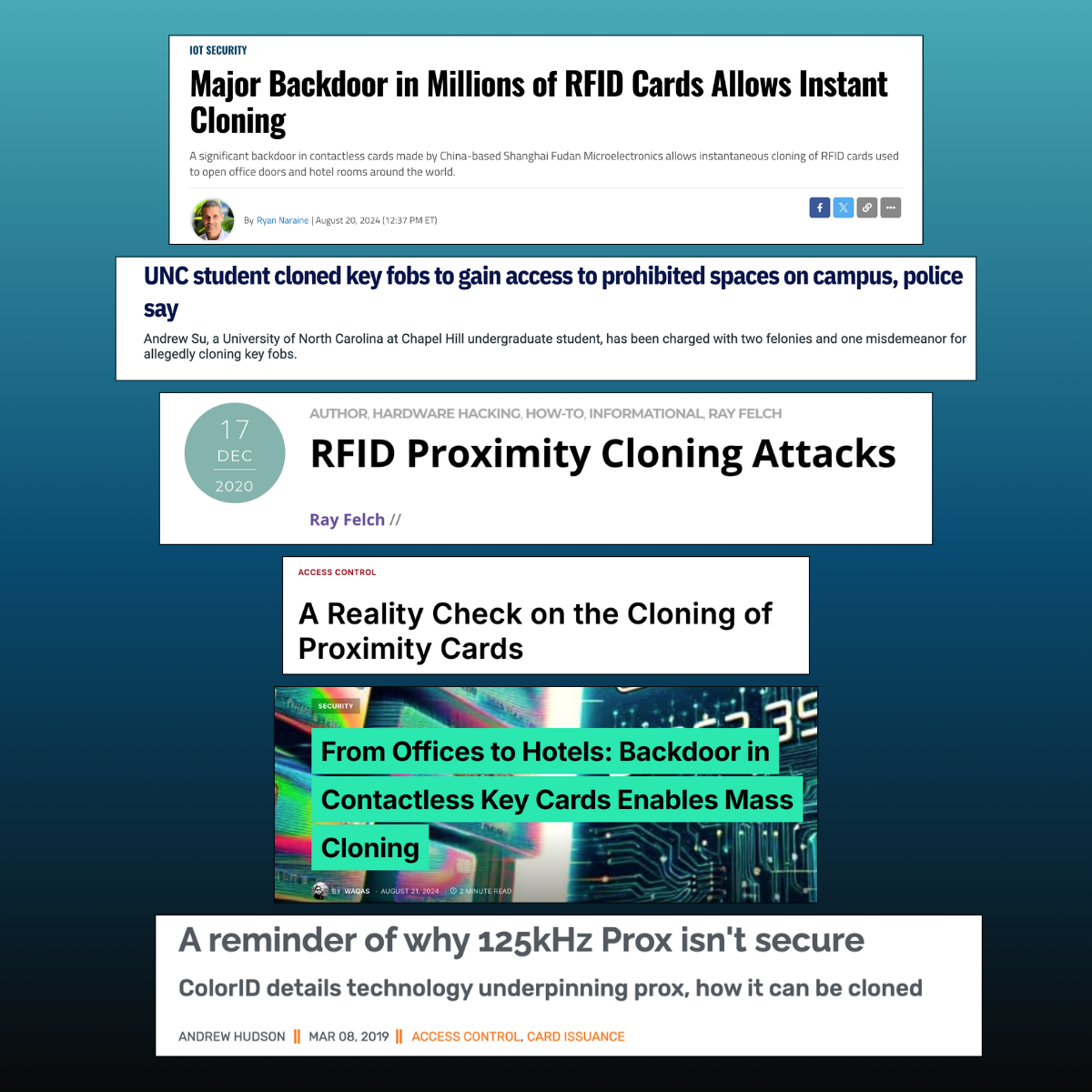
By the early 2000s, the security community had already identified fundamental problems with proximity cards. They're vulnerable to cloning. The encryption standards are weak by modern measures. To solve this problem, end users wanted to manage their own keys to ensure their security, but key management creates operational overhead and vulnerability windows and not all vendors allow end users to manage their own keys.
Yet here we are, decades later, and 45% of organizations still rely on this technology as their primary access control method. Not because security leaders want to. But because the alternative—ripping out readers, replacing credentials, reimplementing systems across dozens or hundreds of locations—felt too risky and too expensive.
The cost of staying stuck became lower than the cost of evolving. And so the industry stayed stuck.
This created a strange market dynamic. New credential technologies emerged—smart cards, mobile solutions, and advanced authentication methods. But none of them could gain meaningful traction because they typically required rip-and-replace. Organizations couldn't justify the disruption for an incremental security improvement.
Meanwhile, the security risk kept accumulating. Each year represented a higher cost of breach, more sophisticated attacks, more regulatory scrutiny. But the switching costs remained the binding constraint.
What Actually Changed: Two Fundamental Breakthroughs
Breaking this dynamic required solving two separate problems simultaneously.
1. A Credential That Doesn't Require a Secret Key
The first breakthrough is LEAF Verified. It's built on public key cryptography—a fundamentally different approach to security than the one way, symmetric encryption that has defined credential security since the 2000s.
Here's what makes this significant: with traditional credentials, security depends on managing encryption keys. Organizations must provision them. Distribute them. Rotate them periodically. Protect them from compromise. If a key is stolen, the entire security infrastructure becomes vulnerable. This has happened as recently as 2025.
With public key cryptography, this burden disappears. Security is embedded directly into the credential chip during manufacturing. There are no keys to manage, no rotation cycles, no distribution logistics. The credential itself is secure by design, not by operational process.
This is architecturally different. It simplifies operations while simultaneously removing vulnerability windows created by key management.
But credentials are only half the problem. The other half is the reader infrastructure.
2. A Reader That Speaks Past and Present Credential Formats
The second breakthrough solves single vendor limitations. The APEX Reader is engineered with extensive credential compatibility with the ability to read credentials from decades past while remaining ready for technologies years in the future.
This is what makes the transition possible. Organizations can deploy LEAF Verified credentials gradually. Legacy prox cards continue working if desired. The system adapts to whatever credential technology is in use at any given moment.
But it goes deeper than just reading multiple formats. The APEX Reader includes engineered tools specifically designed for transition scenarios:
Patented Prox Filter secures legacy prox cards instantly with dual-tech protection, eliminating the vulnerability while you transition credentials. You're not forced to deploy new credentials on day one. This innovation has saved organizations millions in unnecessary infrastructure costs by allowing them to strengthen existing systems without complete replacement.
Patented OSDP Auto-Detect upgrades your security protocol from legacy Wiegand to modern OSDP standards—remotely, using your existing wiring. No reinstallation. No downtime. No need to re-run millions of feet of cable through walls, ceilings, and conduits. Organizations can modernize their security protocols without the massive infrastructure overhaul that previously made upgrades prohibitively expensive.
Together, these two breakthroughs solved the paradox. They set the modern standard for access. For the first time, organizations can transition to modern credential technology without the massive infrastructure replacement costs that previously made it impossible.
Beyond Transition: Building Infrastructure for Longevity
The ability to transition is important. But the real innovation is architectural. This new modern standard is built around a principle that hasn't guided access control design before: infrastructure that evolves rather than replaces.
This changes how you think about access control investment. Most organizations view it as a one-time capital expense—you deploy infrastructure and hope it lasts 10-15 years. Meanwhile, the technology world moves on, and your infrastructure becomes progressively more dated.
With APEX and LEAF Verified, the model is different. The APEX Reader's remarkable credential compatibility means it adapts as technology evolves. Your infrastructure doesn't become obsolete. It becomes more valuable over time—reading legacy formats for backwards compatibility, modern formats for current security, and future formats you don't even know about yet.
This is enabled by several design choices that break from industry convention:
LEAF Verified's NDEF capabilities transform credentials into more than just access badges. They become gateways for personalized experiences—employee onboarding, visitor management, parking integration, building services. As organizational needs evolve, the credential platform evolves with them.
Public key cryptography's inherent interoperability means you're not cornered into a single vendor ecosystem. Multiple manufacturers can build systems that work with LEAF Verified credentials. This is true freedom of choice—a rarity in access control.
Rugged hardware design—metal construction, IP65+ rating—eliminates the premature obsolescence that drives unnecessary reader replacements. The reader is engineered to last decades, not years.
What This Means Across Different Roles
For Security Leaders
You've been trapped between security liability and operational inertia. LEAF Verified eliminates the key management burden that creates vulnerability windows. Public key cryptography means security isn't dependent on operational discipline—it's embedded in the system itself. The APEX Reader lets you transition at a pace your organization can handle, not on someone else's replacement timeline.
For IT Operations
Managing legacy credentials means managing encryption keys. Managing multiple credential types means managing multiple systems. LEAF Verified simplifies this dramatically. One credential type. No key management. And the APEX Reader's compatibility means you're not managing multiple readers for different formats—just one that reads them all.
For Multi-Location Enterprises
You've been managing incompatible systems across facilities. Different vendors. Different credential formats. Different security standards. One unified system that works everywhere eliminates this complexity. Deploy at each location on your timeline. One credential works across all of them.
The Moment When Stalemate Breaks
For two decades, the access control industry has been locked in a paradox. The need for change was obvious. But the cost of change was prohibitive.
That paradox breaks when you solve both problems simultaneously: a credential architecture that doesn't require key management burden, and a reader infrastructure that prevents lock-in through lifetime compatibility.
What emerges is infrastructure fundamentally different from what came before. Not an incremental improvement. An architectural reimagining of how access control should work.
Organizations no longer have to choose between security risk and operational disruption. They can evolve their access control infrastructure on their own timeline, at their own pace, with their own budget constraints.
Twenty years of being stuck is long enough. The technology is finally ready to move forward. The question is: will your organization move with it?
Learn more about how LEAF Verified and the APEX Reader work together to create an evolved access solution.

.png)

.png)


.png)